FAANGs have amassed giant, uniquely priceless datasets from users and are successfully monetizing this knowledge, additional reinforcing the limitations to entry and fortifying their business Technology moats from assault. They have also efficiently exploited the disruptive technologies of the most recent computer technology period, cellular, and cloud.
Catboo plus pics of my cats /ᐠ .ᆺ. ᐟノ@Ranboosaysstuff #cats4ranboo #ranboofanart
I drew this by the way with a computer mouse. pic.twitter.com/zHXfhsQ55K— Spooky The Cat Gaming Wasn't Taken (@SpookyTheCatCCC) May 6, 2021
This new technology is undoubtedly the one that can singularly have the most far-reaching effects on crew systems in each the close to time period and the long run. However, in 2010, solely a handful of chosen textile attire computer techniques remained, because of consolidation, mergers and acquisitions among the vendors. The computer applied sciences Computer & Technology used for designing textiles have established their own features. As computers discover their means into more and more services and products, individuals who examine Computers and Technology are finding that they are in demand in every trade.
Undergraduate Levels Awarded
The information and computer technology program prepares the way forward for IT, be it working for a authorities agency or a non-public company. The National Security Agency has acknowledged this program as a National Center of Excellence in Information Assurance Education.
- Valencia’s certificates applications can put you on the quick-track to reaching your career objectives.
- In each department of engineering, prior to the implementation of CAD, design has traditionally been completed manually on the drawing board.
- Graduate and post-graduate students search the Master of Science in Computer Science , Doctor of Computer Science , or PhD in Computer Science.
Submit scanned copies of official or unofficial transcripts from all establishments attended to the Graduate College. Upon admission, last official transcripts from every diploma granting institution have to be submitted. This is a pattern of a course sequence for a cohort that begins in Fall semester. The first 6 courses are these for the Computer Technology Endorsement Certificate. Three instruments from VMware’s portfolio — Workspace One, Carbon Black Cloud, and SASE — are actually bundled, providing a set of tools to simplify management of remote worker gadgets and functions. Mozilla continues to push privacy protections in Firefox 88, which prevents the window.name property from leaking information across sites. The simply-published patent describes a characteristic that generates an employee “anxiousness rating” primarily based on information similar to blood pressure and coronary heart rate, suggesting when workers must take a break.
Accepted Scholar Assets
Our applications put together graduates who’re proficient in the latest computer technology. Specifically, we focus on helping you get the proper data where you need it, and make it useful in your context – slightly thing we wish to call “knowledge engineering”. We supply a variety of complimentary, seamlessly integrated providers to companion with you to strategize the best course and implement the adjustments to achieve your data objectives. Students end the course ready for postsecondary education Computer and coaching, and a successful profession in information technology. The mission of the Computer Occupations Technology diploma is to prepare college students for entry-level employment normally or broad computer occupations or as an adjunct skill in a different occupation. Nexsan is looking at storage in a totally new way with itsUNITY™ unified information storage platform. Easy to know resources that will help you train engineering concepts to college students at all levels.
What are the types of computer courses?
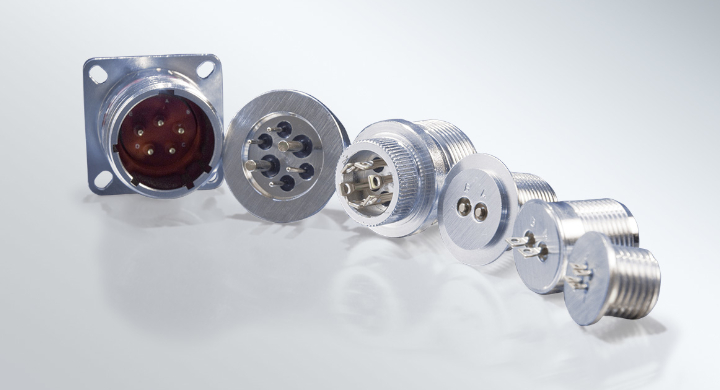
Quite simply, computer hardware is the physical components that a computer system requires to function. It encompasses everything with a circuit board that operates within a PC or laptop; including the motherboard, graphics card, CPU (Central Processing Unit), ventilation fans, webcam, power supply, and so on.
Image-processing techniques together with knowledge analytics instruments for medical images are used for the aim of analysis of biological data. Virtual reconstruction of organic parts similar to skulls can be carried out for requisite research. Artificial intelligence methods are utilized in cognitive psychology for the purpose of better understanding human ideas.
Student Enrolment And Graduation
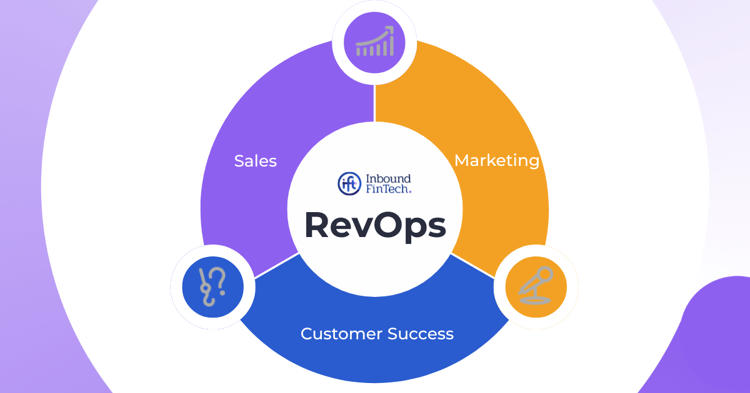
The rise of Big Data has created a major demand for analysts and directors who can handle databases, while the monetary worth of data has made Information Security/Cybersecurity a very hot commodity. For areas like Web Design or Programming, a healthy number of nice art and design lessons can help offer you a perspective on image, construction, and form beyond what you get in digital design programs. The Networking and Cybersecurity Option is meant to organize people to put in, configure, and assist a company’s network. Applying the Theoretical Domains Framework to identify obstacles and focused interventions to boost nurses’ use of electronic treatment management methods in two Australian hospitals. Clinical decision help helps the pharmacy division of a South Carolina medical middle automate monitoring of medicine effectiveness. Computer technology includes increasing existing computer capacities.
On any given day, B&H has as many as 1200+ several types of computer systems for sale, not to mention computer equipment, parts and peripherals like monitors, mice, keyboards, power cords, webcams and more. We also have a whole Used Department specializing in open field computer deals, like-new returns and refurbished computer systems that may save you a bundle. Oklahoma summers may be brutal, one-hundred-diploma warmth, scorching sun and if your air conditioner isn’t working, you’re miserable.



More Stories
The Future of Business: Key News to Watch
This Week’s Business News: What’s Trending Now
The Latest Business News You Need to Know