[ad_1]
Drupal issued a stability advisory of four essential vulnerabilities rated from reasonably vital to important. The vulnerabilities impact Drupal versions 9.3 and 9.4.
The protection advisory warned that the different vulnerabilities could let an hacker to execute arbitrary code, putting a web site and server at danger.
These vulnerabilities do not have an impact on Drupal edition 7.
Furthermore, any versions of Drupal prior to 9.3.x have achieved Conclusion of Everyday living status, which usually means that they are no lengthier receiving stability updates, creating them dangerous to use.
Essential Vulnerability: Arbitrary PHP Code Execution
An arbitrary PHP code execution vulnerability is just one in which an attacker is capable to execute arbitrary commands on a server.
The vulnerability unintentionally arose due to two security options that are supposed to block uploads of perilous information but unsuccessful due to the fact they didn’t purpose very well with each other, ensuing in the present significant vulnerability which can outcome in a distant code execution.
“…the protections for these two vulnerabilities earlier did not function accurately with each other.
As a consequence, if the web-site were configured to allow for the add of files with an htaccess extension, these files’ filenames would not be adequately sanitized.
This could enable bypassing the protections presented by Drupal core’s default .htaccess files and attainable distant code execution on Apache web servers.”
A remote code execution is when an attacker is capable to operate a destructive file and acquire about a website or the full server. In this individual instance the attacker is equipped to assault the world wide web server itself when functioning the Apache internet server application.
Apache is an open up source world wide web server program upon which all the things else like PHP and WordPress operate. It is basically the computer software component of the server alone.
Accessibility Bypass Vulnerability
This vulnerability, rated as moderately Critical, allows an attacker to change facts that they’re not intended to have accessibility to.
According to the stability advisory:
“Under specified circumstances, the Drupal main form API evaluates type ingredient entry incorrectly.
…No forms furnished by Drupal main are identified to be vulnerable. Even so, types additional through contributed or custom made modules or themes could be influenced.”
Multiple Vulnerabilities
Drupal printed a complete of four protection advisories:
This advisory warns of many vulnerabilities influencing Drupal that can expose a internet site to different kinds of assaults and results.
These are some of the probable concerns:
- Arbitrary PHP code execution
- Cross-internet site scripting
- Leaked cookies
- Entry Bypass vulnerability
- Unauthorized details access
- Info disclosure vulnerability
Updating Drupal Encouraged
The protection advisory from Drupal advisable quickly updating variations 9.3 and 9.4.
End users of Drupal version 9.3 should really update to variation 9.3.19.
Users of Drupal variation 9.4 should really up grade to edition 9.4.3.
Quotation
Drupal main – Vital – Arbitrary PHP code execution
Featured graphic by Shutterstock/solarseven
[ad_2]
Resource connection



More Stories
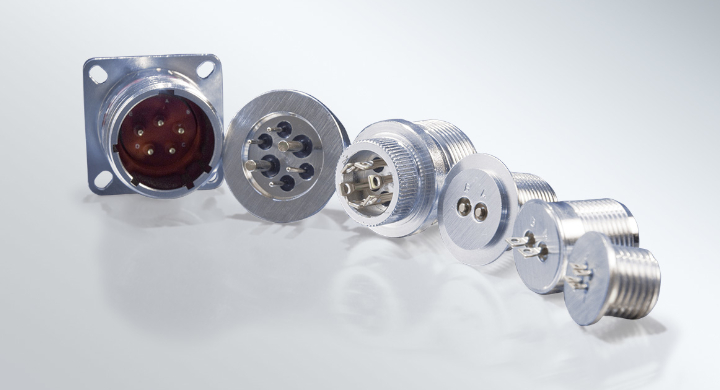
Custom Hermetic Feedthrough Solutions for Challenging Environments
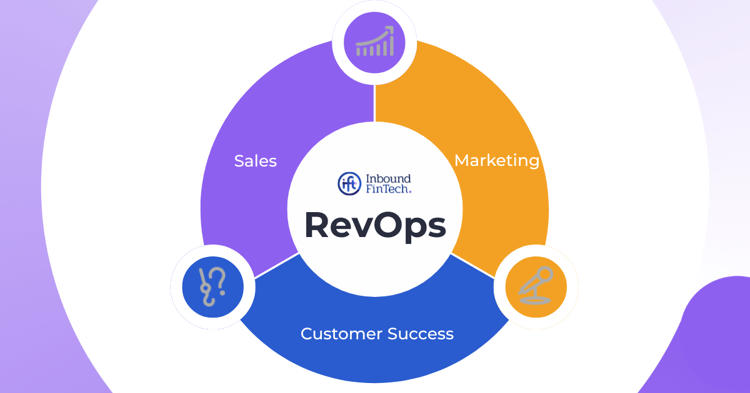
Scaling Your Digital Operations with a CMS for Media Companies
The Importance of Lighting and Layout in Trade Show Fabrication